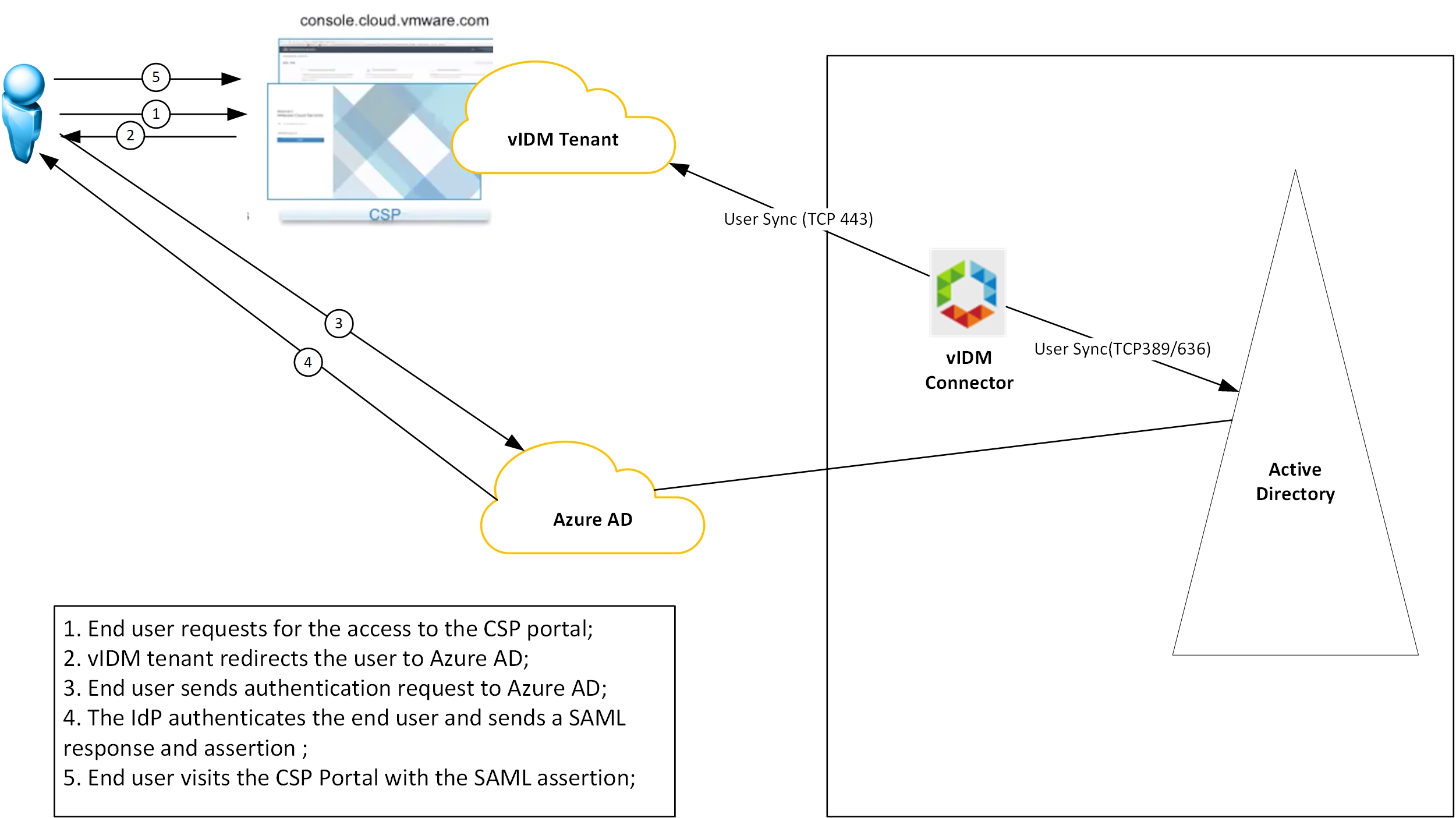
The Federated Identity feature of VMware Cloud on AWS can be integrated with Microsoft Azure AD as well. In this integration model, the customer dedicated vIDM tenant will work as the SAML Service Provider and the Azure AD will work as the IdP.
Disclaimer:
- The Azure AD settings in this blog are to demo the integration for vIDM, which may not be the best practise for your environment or meet your business and security requirements.
- VMware Cloud on AWS has begun to support self-service enterprise federation setup since Oct 2021. The set-up UI is different from what the blog shows but the configuration is essentially the same. Please update the settings accordingly based on the latest UI.
Note: If you would like to use the vIDM connector for users/groups sync, please complete the vIDM connector installation and the vIDM tenant basic setup as per my first blog of this series (https://davidwzhang.com/2019/07/31/setting-up-federated-identity-management-for-vmc-on-aws-install-and-setup-vidm-connector/) before continuing.
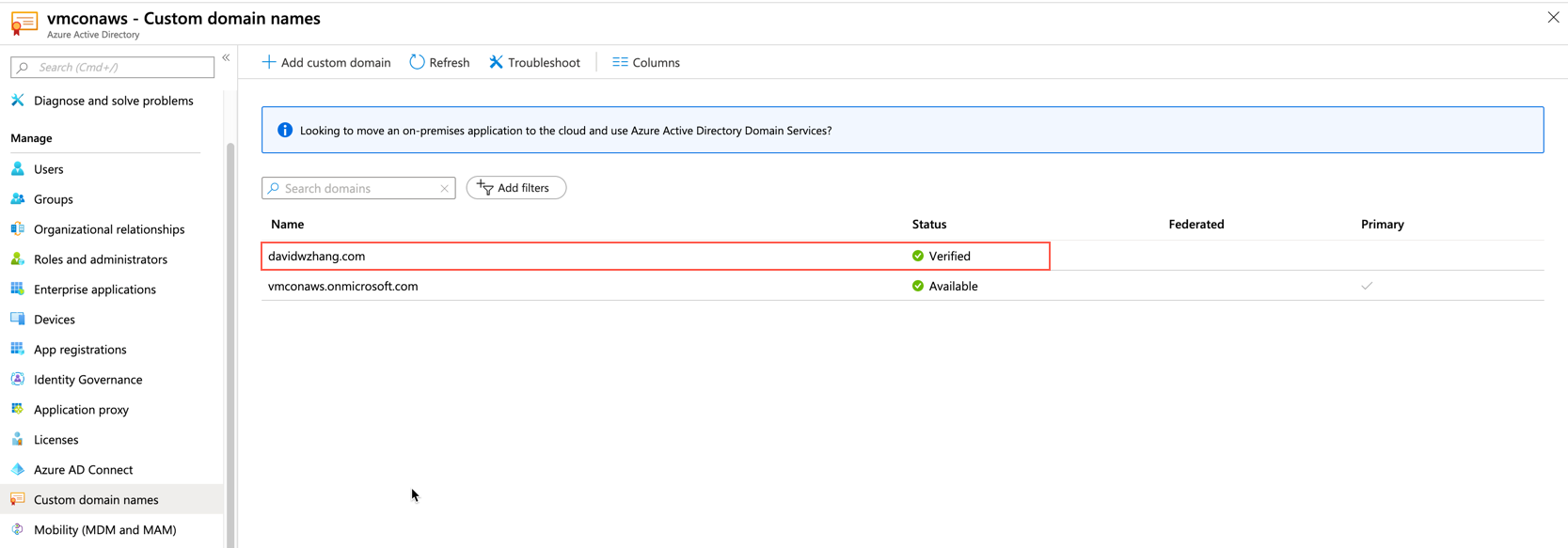
The AD domain name for this blog is davidwzhang.com.
Prerequisite
- The on-prem domain has been added as a custom domain under your default Azure AD.
- Azure AD PREMIUM (P1 or P2) feature is enabled.
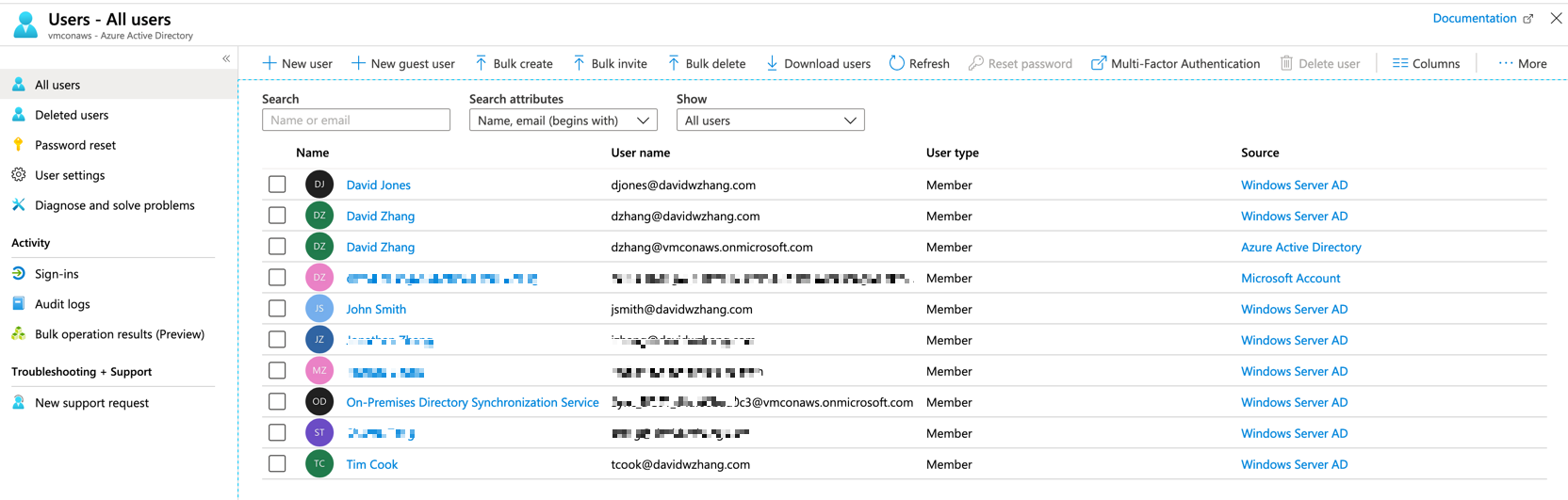
- On-prem AD users/groups are synced with Azure AD.

Step 1: Add Azure AD as an IdP
First, login to your Azure Portal https://portal.azure.com and select Azure Active Directory.
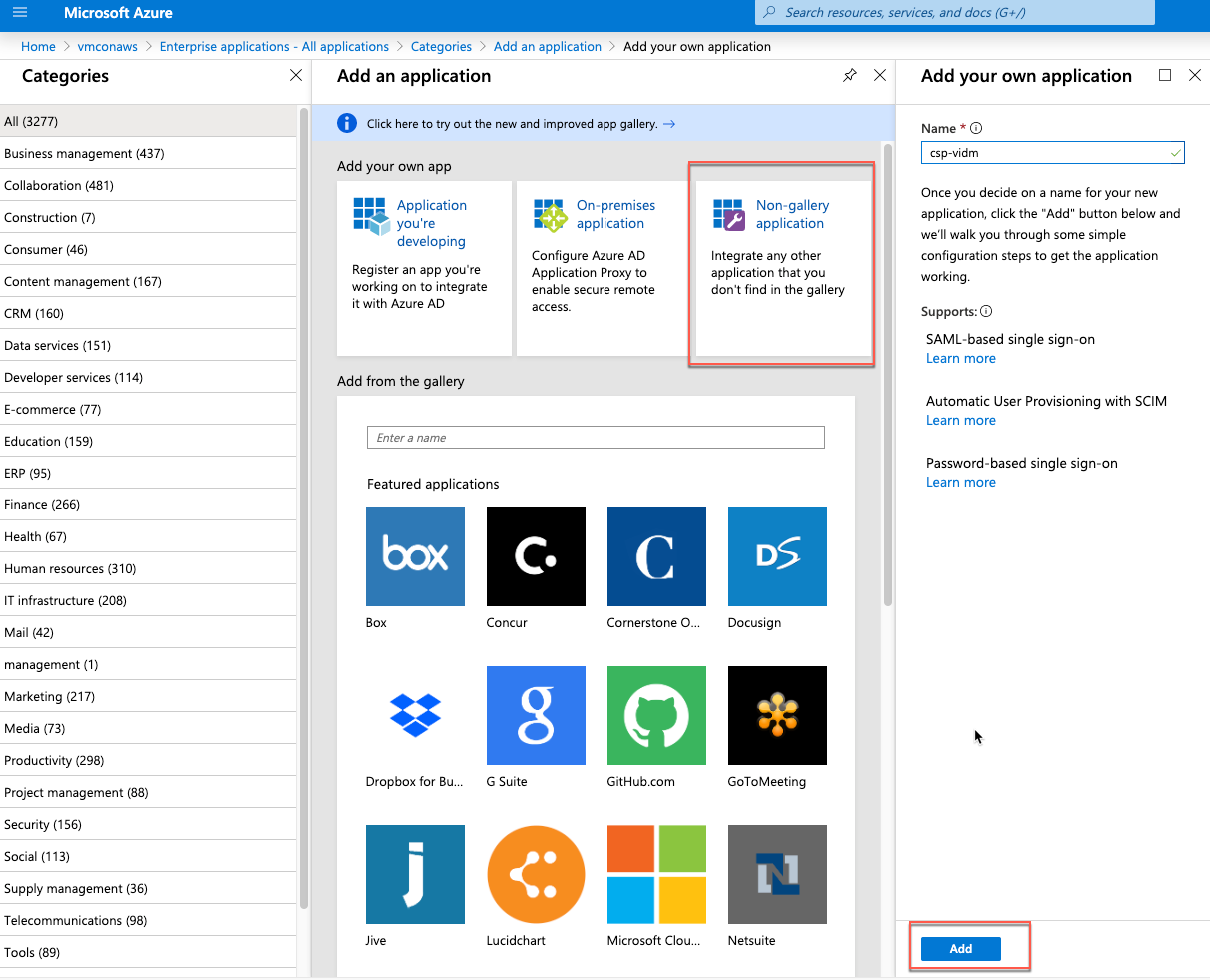
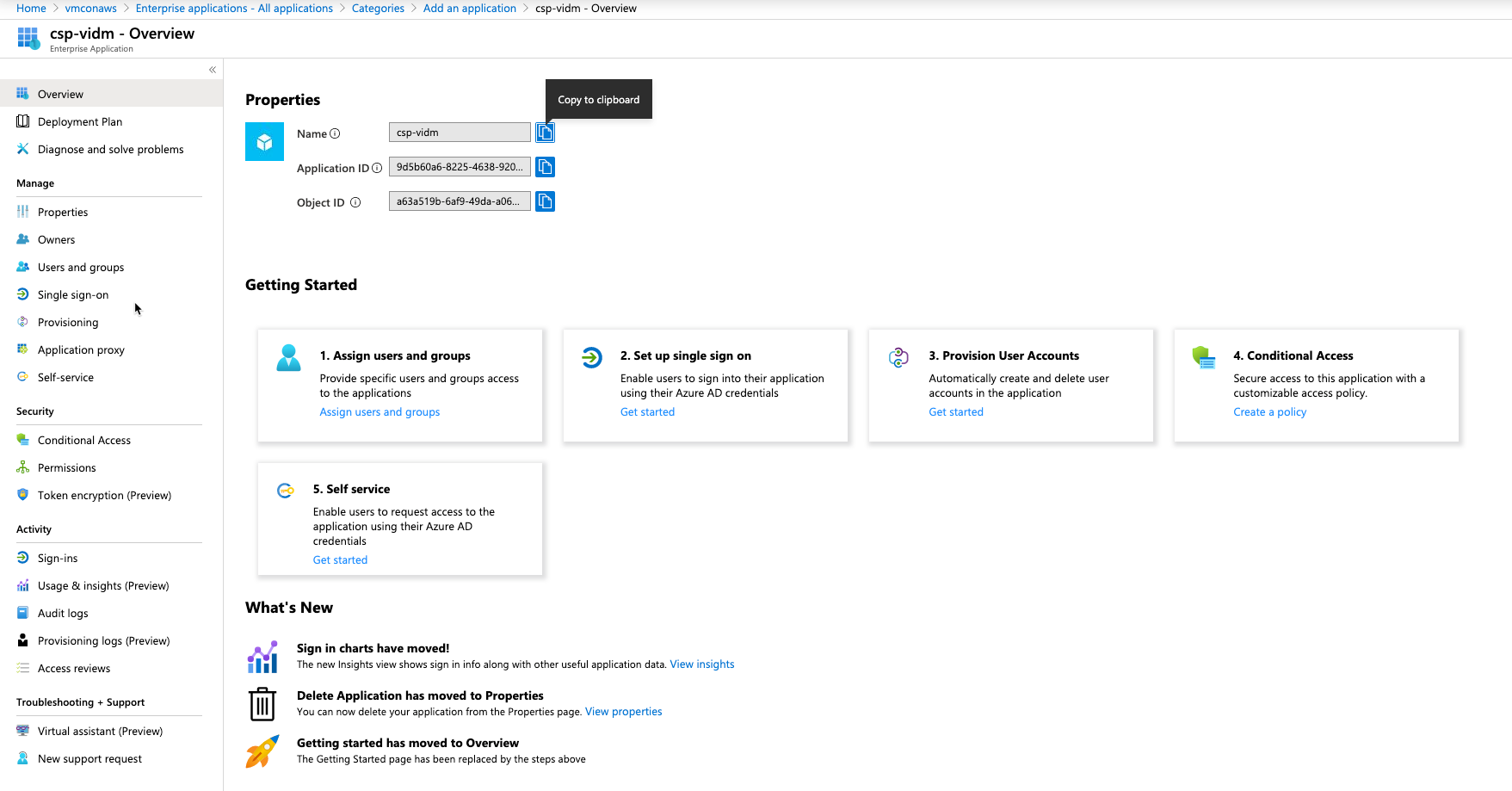
Find “Enterprise Applications” in the list under my default Azure Active Directory (vmconaws) and then create a “New Application”. In the “Add your own app” window, select “Non-gallery application” and input the application name “csp-vidm” and click the “Add” button as below.
In the popped up “Enterprise Application” window, select “Set up single sign-on” under “Getting Started”.
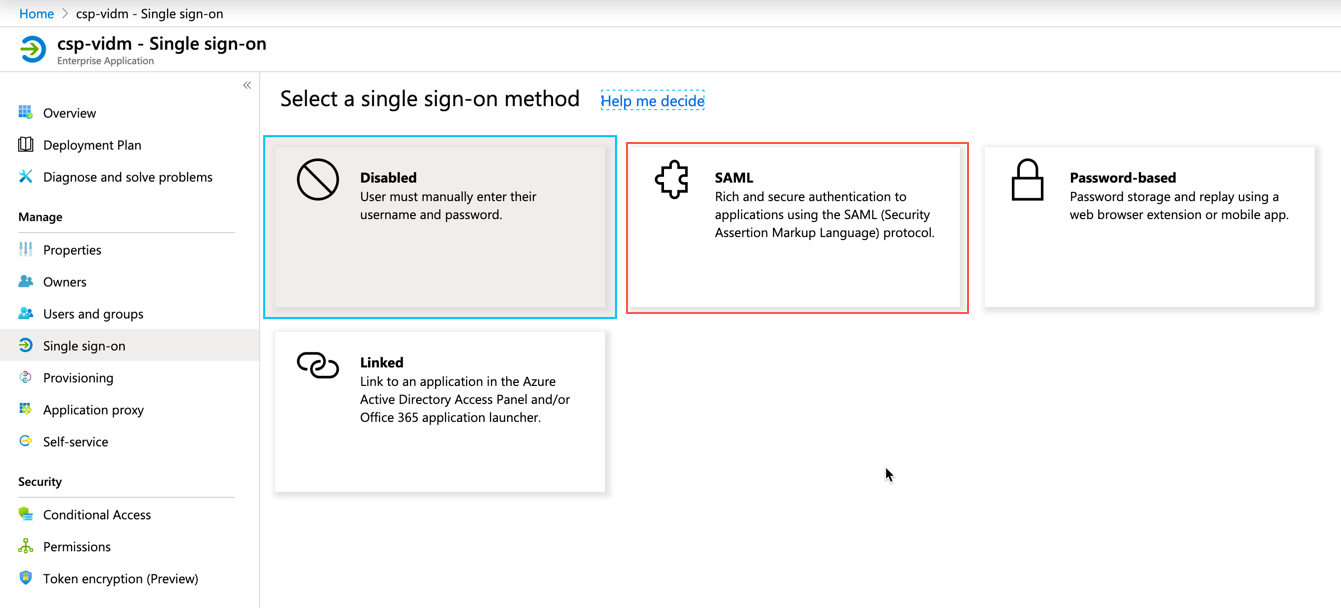
In the pop-up “Select a single sign-on method” window, select SAML.
Next, click the Download hyperlink to download the Azure AD federation metadata XML file or copy the App Federation Metadata URL.
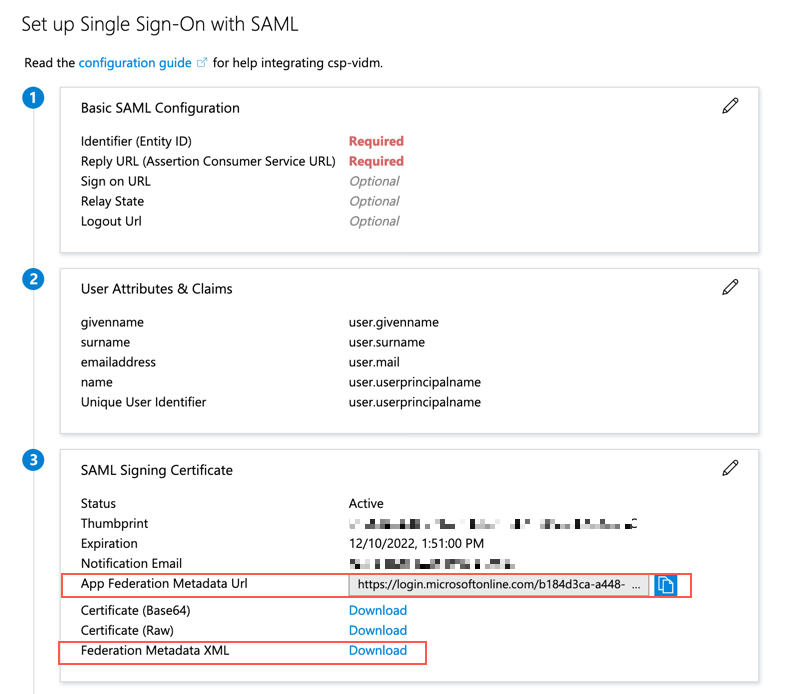
Now we have to pause here. You may have noticed that we still have two pending SAML configuration items: Identifier (Entity ID) and Reply URL (Assertion Consumer Service URL). We will come back to complete these items once we get the required SAML Service Provider metadata from the vIDM tenant.
Step 2: Create an Identity Provider in vIDM Tenant
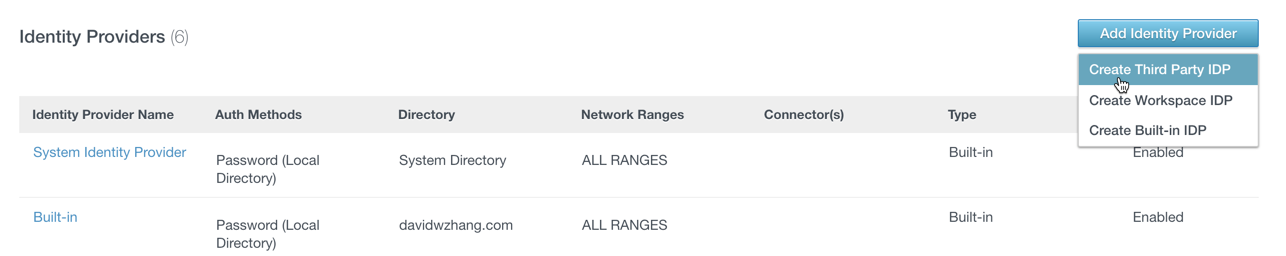
Go to the vIDM tenant administrator console and click “Add Identity Provider” and select “Create Third Party IDP” within the “Identity & Access Management” tab.
Input the parameters as below:
- Identity Provider Name: AzureAD
- SAML AuthN Request Binding: HTTP Redirect
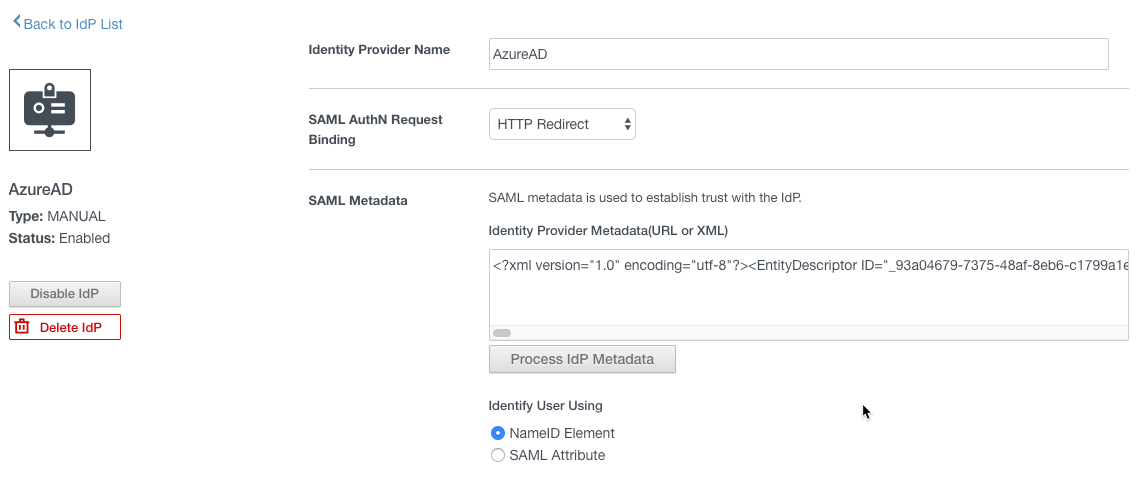
In the SAML Metadata section, copy the content of downloaded Azure AD federation metadata XML file to the text box of Identity Provider Metadata(URL or XML) then click the button “Process IdP Metadata”.
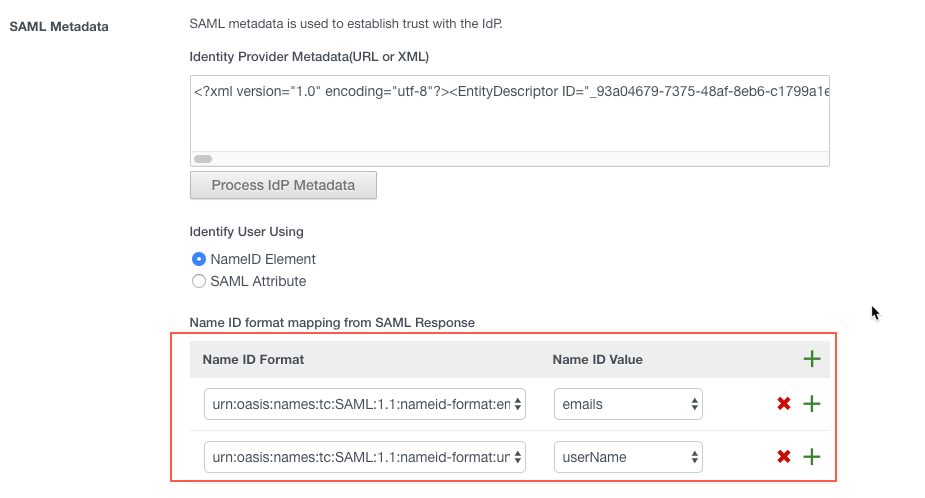
Next, add two Name ID format mappings as the below:
- urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress = emails
- urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified = uerName
Then from the dropdown of the “Name ID policy in SAML request (Optional)”, select “urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress”

The rest of the settings are as below:
- Just-in-Time User Provisioning: Disabled
- Users: davidwzhang.com
- Network: ALL Ranges
- Authentication Methods
- Authentication Methods: AzureADPassword
- SAML Context: urn:oasis:names:tc:SAML:2.0:ac:classes:Password
- Single Sign-Out Configuration: Disabled

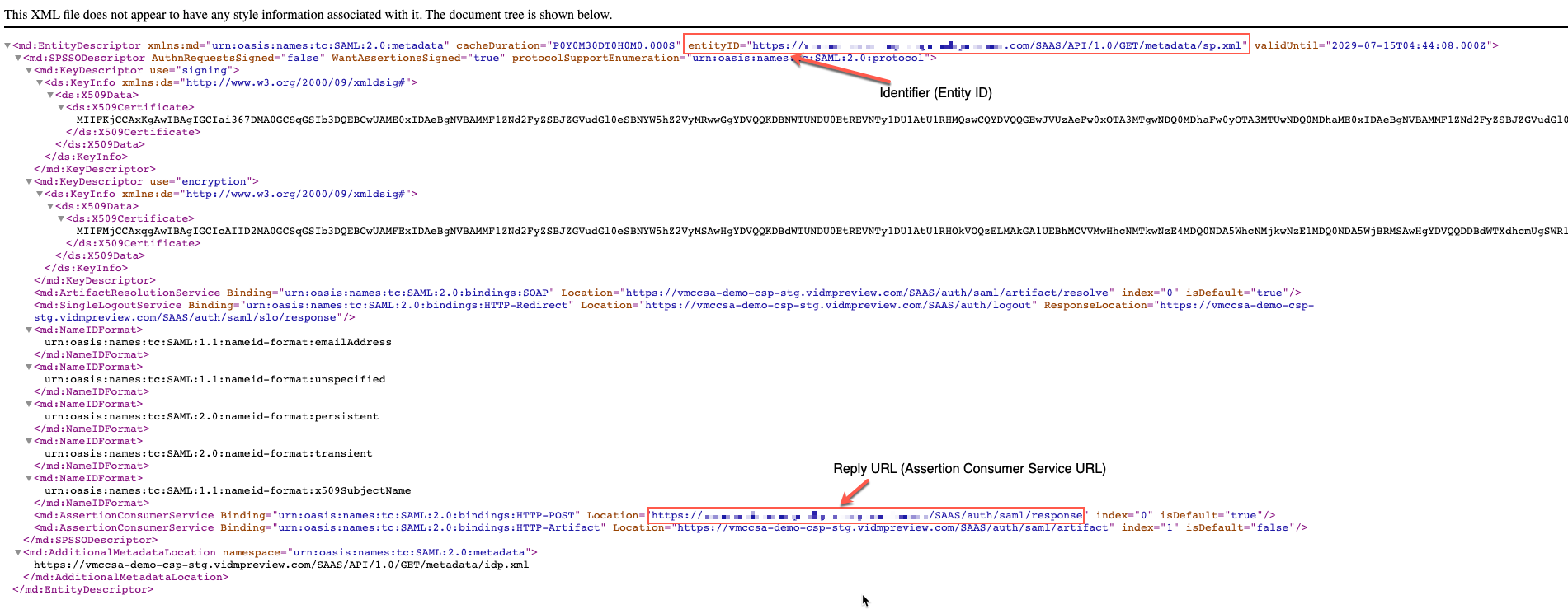
Then click the hyperlink of “Service Provider (SP) Metadata” to open the SAML Service Provider metadata in a browser. Then you can find the Identifier (Entity ID) and Reply URL (Assertion Consumer Service URL) which are required to complete the Azure AD IdP SAML setup.
Now, click the “Save” button to save the IdP setup.
Step 3: Add SAML Information for Azure AD
Go back to Azure Portal and continue the Single Sign-on SAML setup.
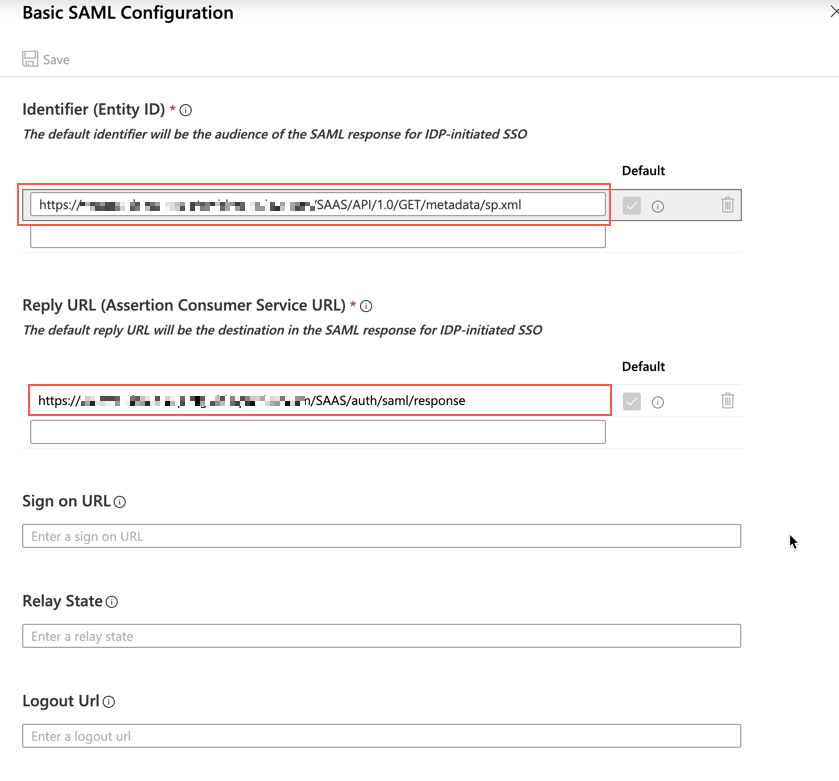
Edit the basic SAML configuration.
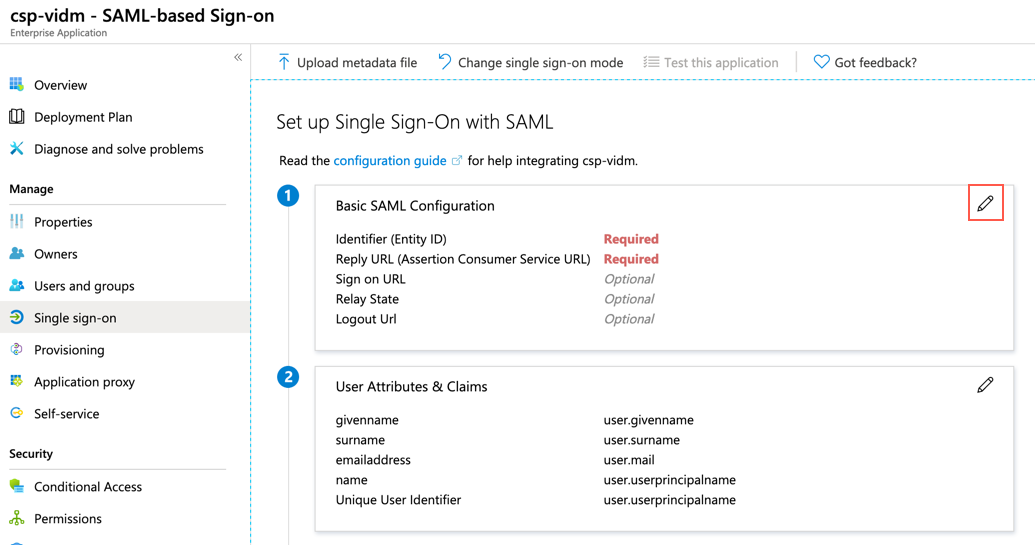
Copy the Identifier (Entity ID) and Reply URL (Assertion Consumer Service URL) which we got in the last step, to the corresponding text box and save the configuration.
Next, add user groups which are granted access to the VMware Cloud service console to this newly created application. Here two groups (sddc-admins and sddc-operators) are added.
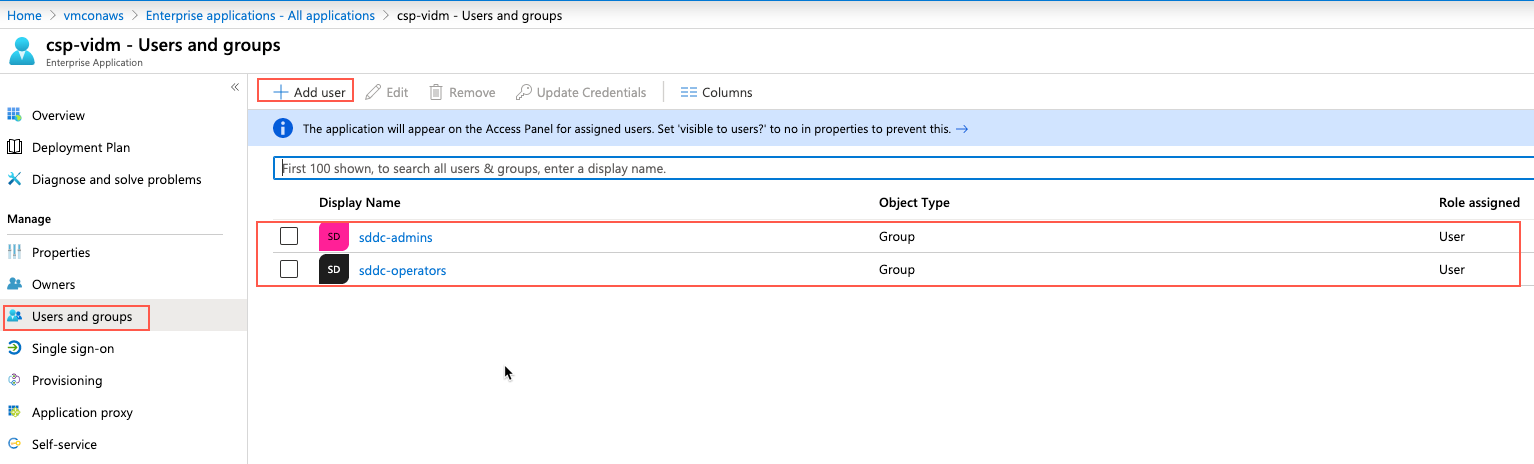
Now we have finished the configuration of Azure AD IdP.
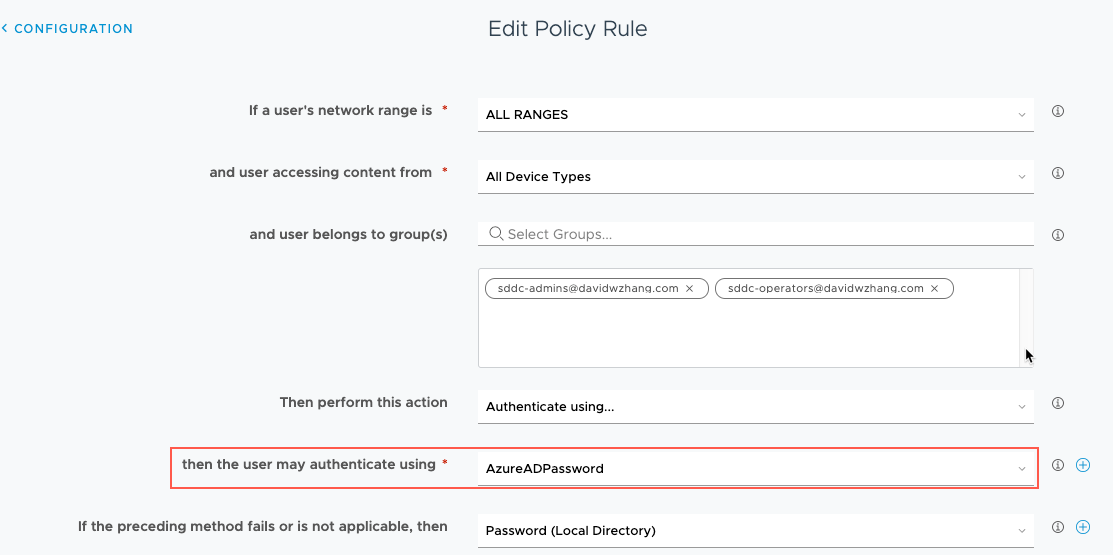
Step 4: Update Authentication Policy
Update the vIDM tenant’s default access policy to include AzureADPassword as the first authentication method.
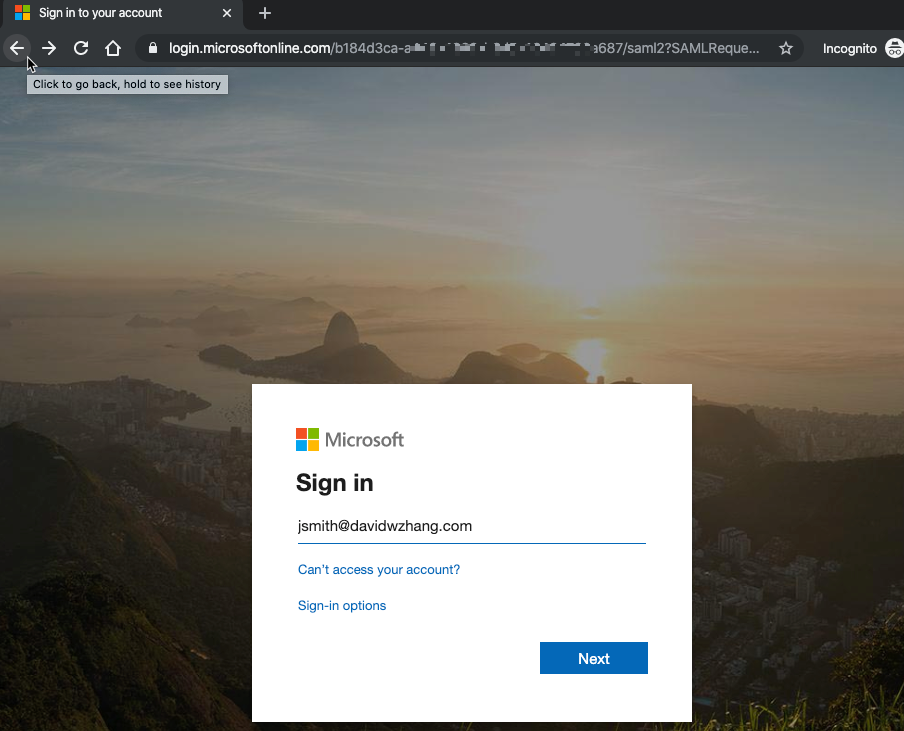
Now, when you try to log into the VMware Cloud service console with your AD account, your login session will be redirected to the Azure AD as below, which authenticates your session.

Pingback: Setting Up Federated Identity Management for VMC on AWS – Install and Setup vIDM Connector – InsidePacket
Pingback: Setting Up Federated Identity Management for VMC on AWS – Authentication with PingOne – InsidePacket